Flock9
Suite
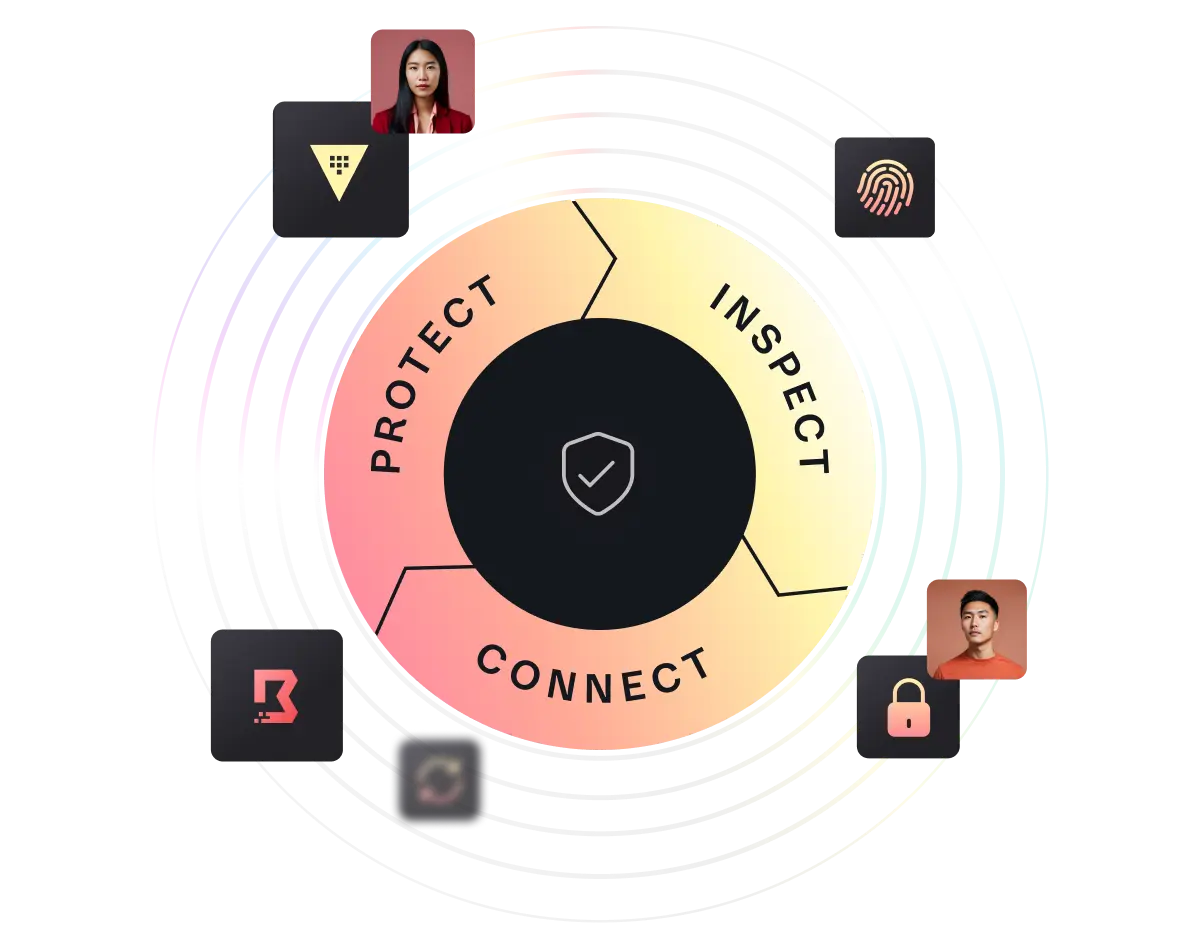
How are you mitigating cloud risk? As your cloud use grows, so does your attack surface. Protect, inspect, and connect the sensitive elements across your cloud infrastructure to reduce credential exposure, enforce least-privileged access, and stop secret sprawl.
1 solution in multiple bricks
All you need to Discover, Backup, Build, Test & Automate your Infrastructure
PRODUCTS
DISCOVER
Guard sensitive data across all environments with a central system of record to reduce the risk of credential exposure.
Securely store secrets, certificates, and keys
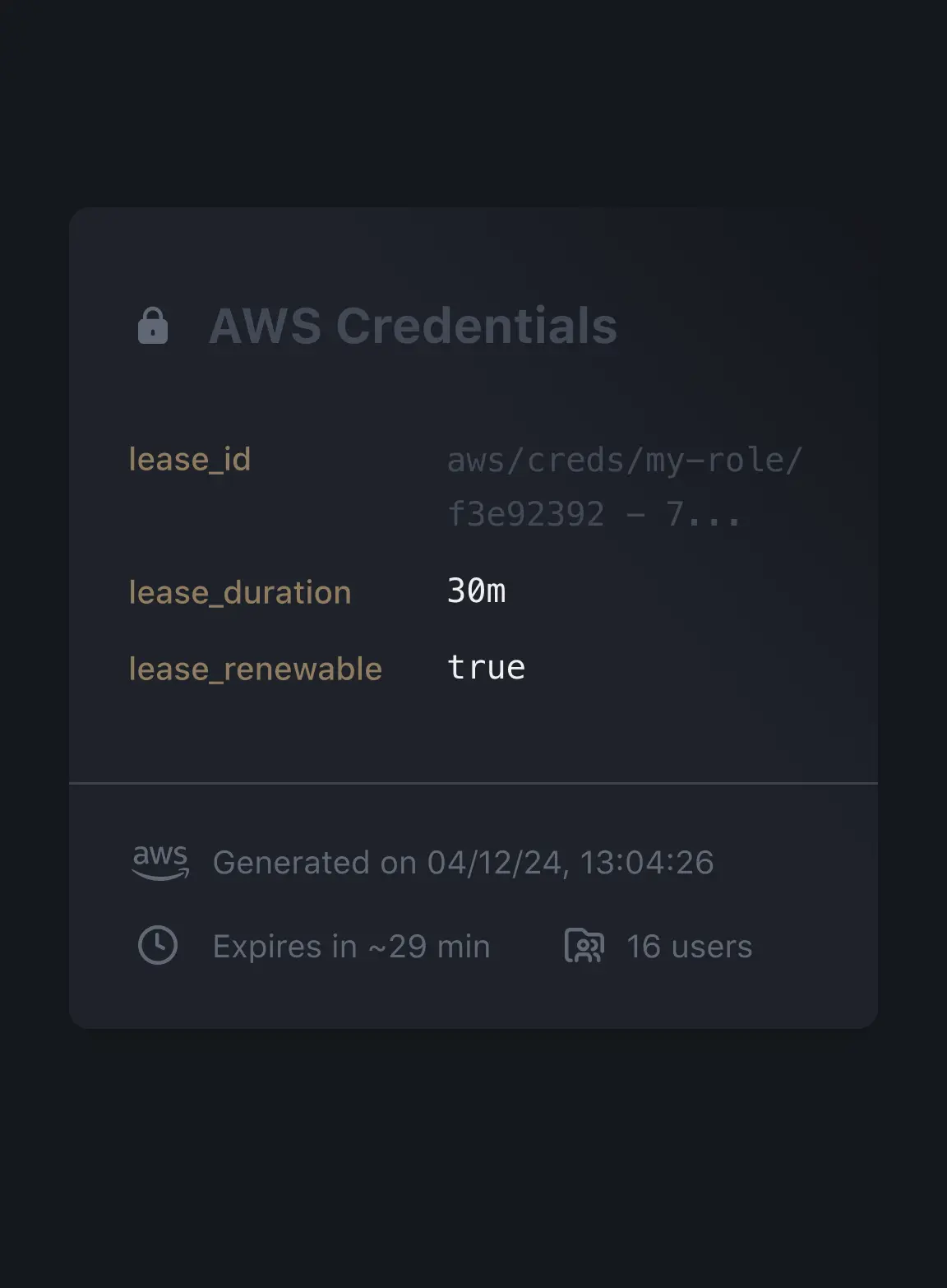
Automatically rotate secrets or create just-in-time dynamic credentials for machines and users
Define policies for access levels based on machine, user, and service identity
Record and audit all access points to sensitive applications
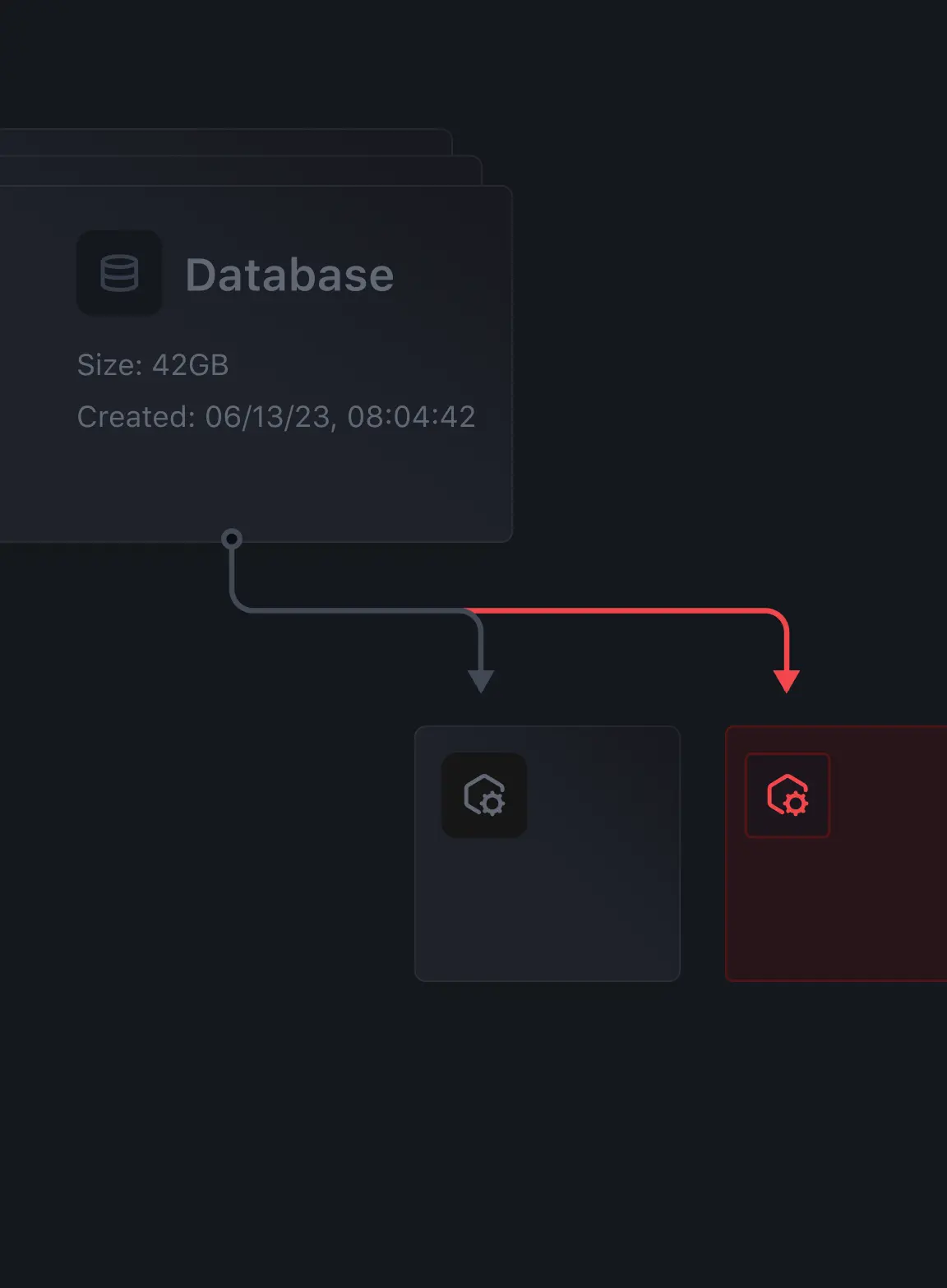
BACKUP
Continuously scan your environment for unsecured sensitive data and keep tabs on privileged access.
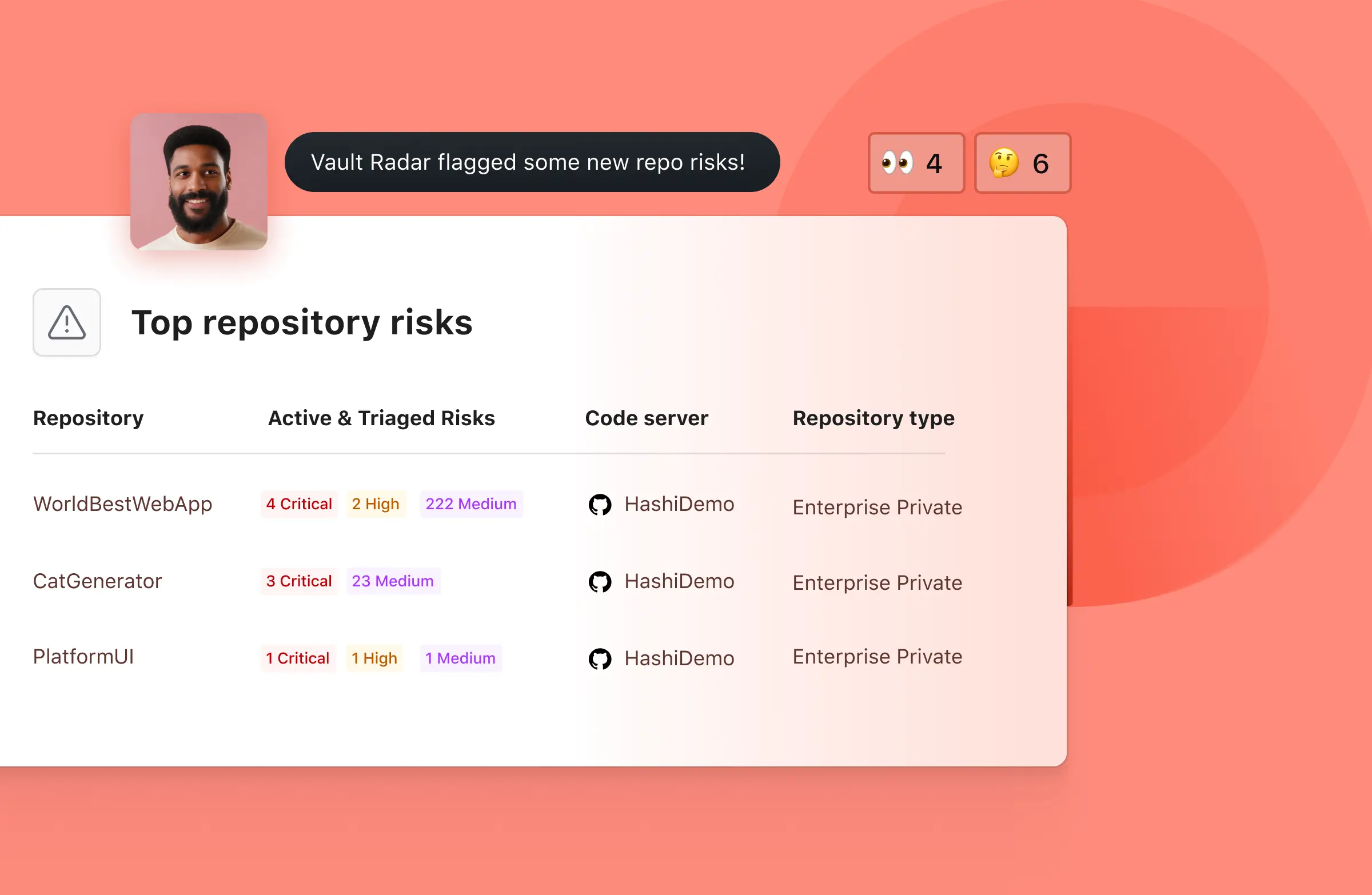
Scan developer repositories to identify exposed secrets and prioritize remediation based on risk
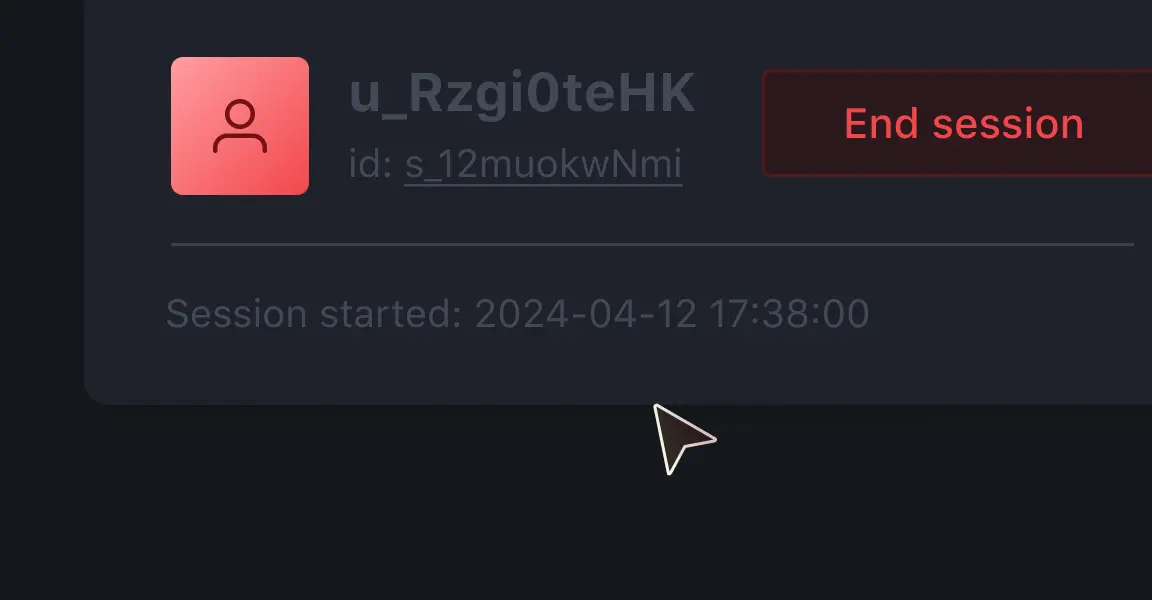
Monitor all privileged access sessions with the option to terminate as needed
Centralize a directory of services and their health statuses with multi-cloud and multi-platform registries
BUILD
Enforce least-privileged access based on trusted identities without exposing your network.

Authenticate and authorize every request for machine-to-machine, human-to-machine, and service-to-service access
Integrate with your preferred identity access management active directory providers for authentication
Limit machine, application, and service access based on policies and roles
TEST & VALIDATE
Enforce least-privileged access based on trusted identities without exposing your network.

Authenticate and authorize every request for machine-to-machine, human-to-machine, and service-to-service access
Integrate with your preferred identity access management active directory providers for authentication
Limit machine, application, and service access based on policies and roles
AUTOMATE
Continuously scan your environment for unsecured sensitive data and keep tabs on privileged access.
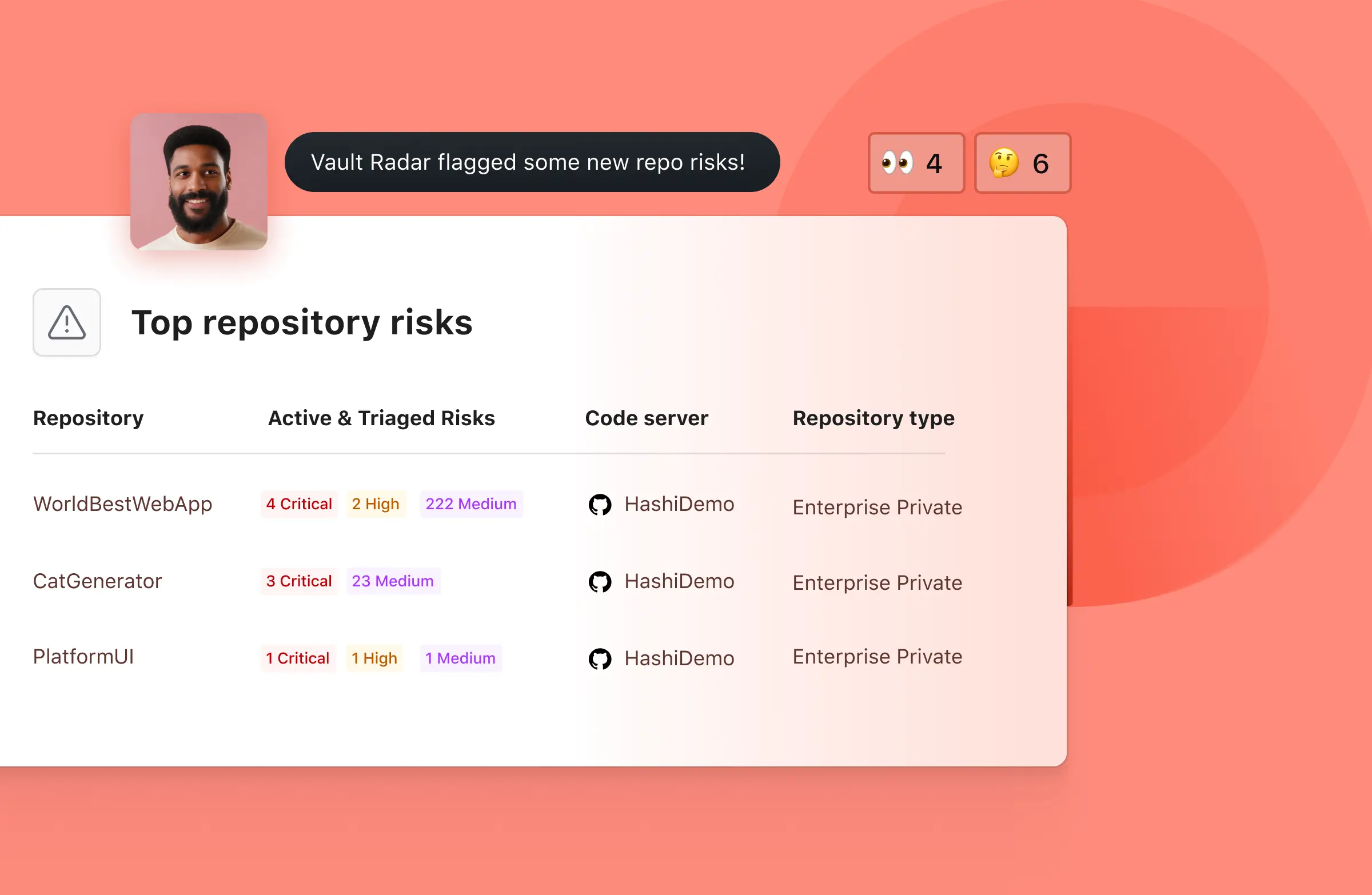
Scan developer repositories to identify exposed secrets and prioritize remediation based on risk
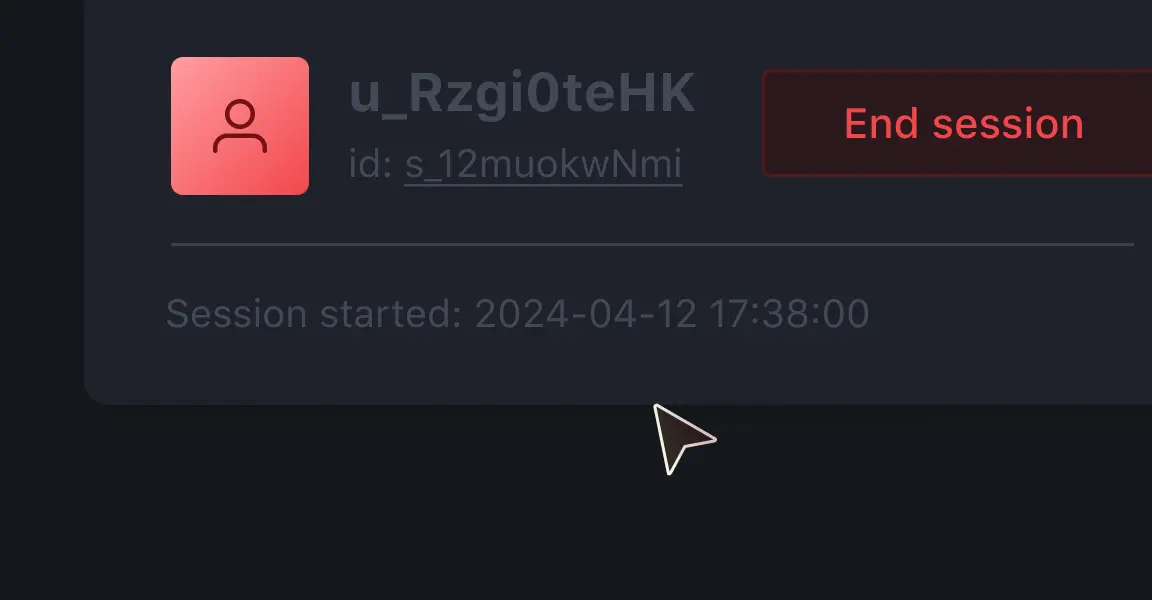
Monitor all privileged access sessions with the option to terminate as needed
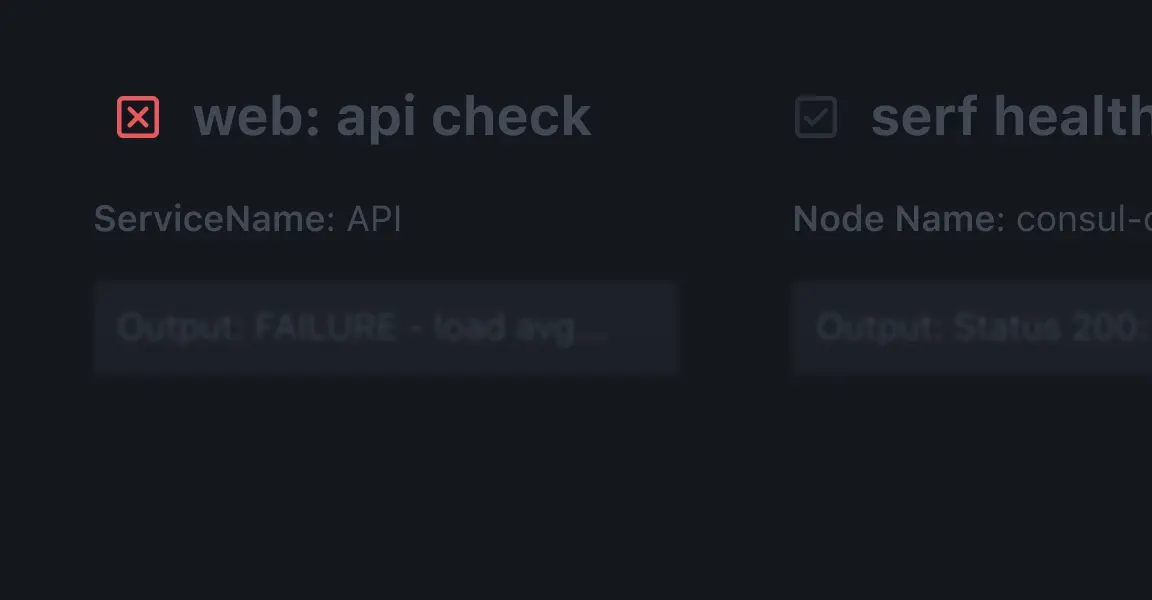
Centralize a directory of services and their health statuses with multi-cloud and multi-platform registries
No more large & complex application. But Modular in pieces you need.
Identity-based security
Use trusted identities to automate access to secrets, data, and applications.
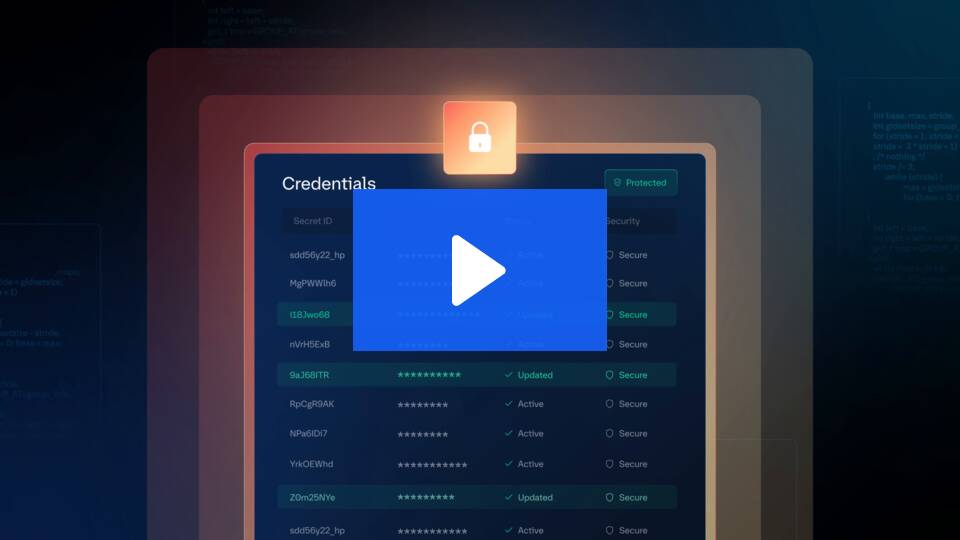
Security system of record
Centrally store and protect secrets across clouds and applications.
Lifecycle management
Gain a complete view of your credentials for proper oversight, rotation, and expiry.
Any questions?
Ready to take the next step? Connect with us or get started today for free with the Flock9 Suite.
