Identity-based security
Use trusted identities to automate access to secrets, data, and applications.
Security system of record
Centrally store and protect secrets across clouds and applications.
Lifecycle management
Gain a complete view of your credentials for proper oversight, rotation, and expiry.
Boundary
Standardize secure remote access
Built for cloud, modern privileged access management from HashiCorp Boundary uses identity-driven controls to secure user access across dynamic environments.
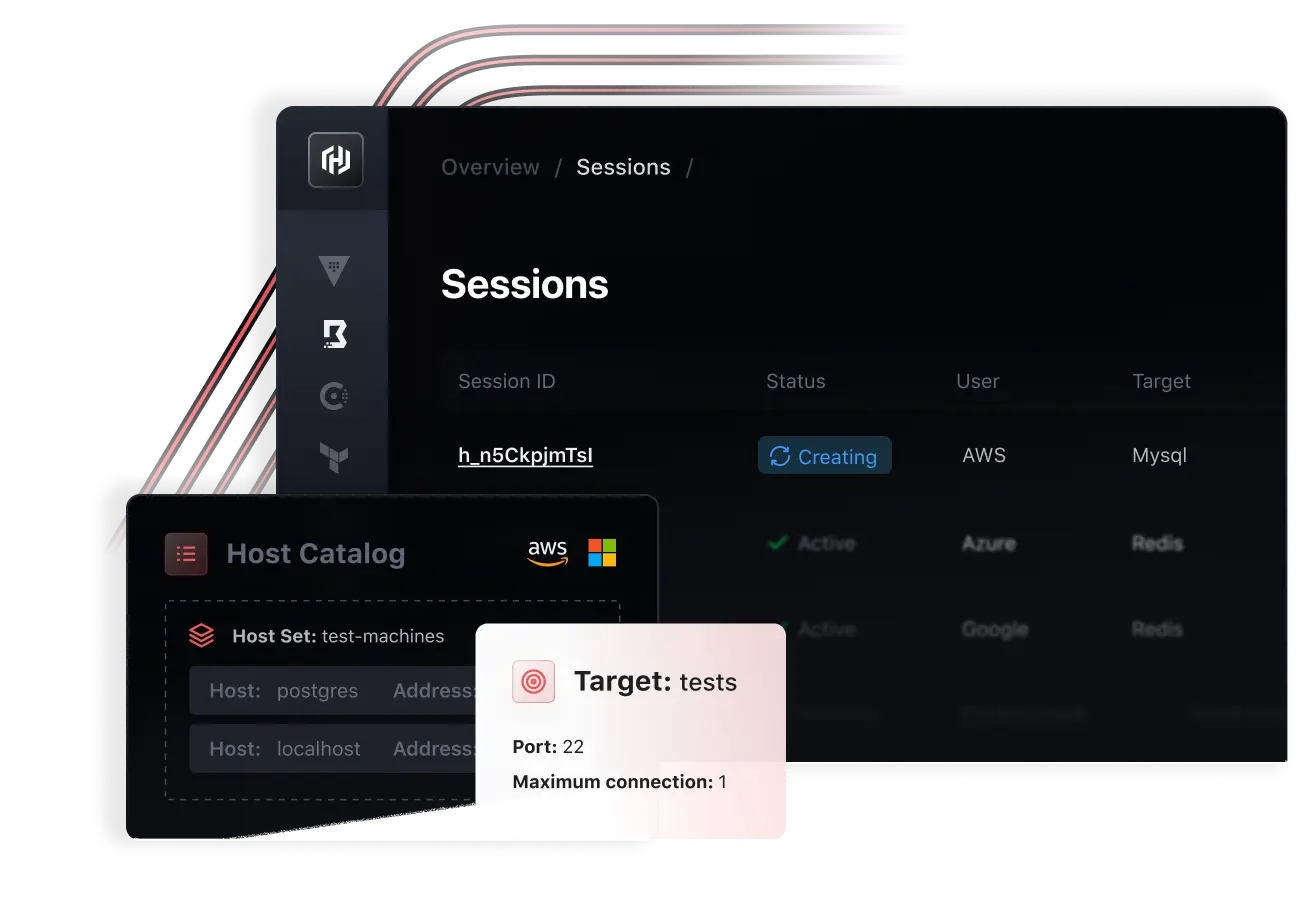
Service-based authorization
Use trusted identity to enforce least-privileged service access based on user roles.
Automated workflows
Manage access for end users and administrators with passwordless credential injection and automated target discovery.
Reduce risk exposure
Replace long-lived credentials with dynamic secrets and just-in-time credentials using Vault.
Consul
Service networking to discover and securely connect your services
HashiCorp Consul provides identity-based service networking for service discovery, secure communication, and network automation across multiple cloud and runtime environments.
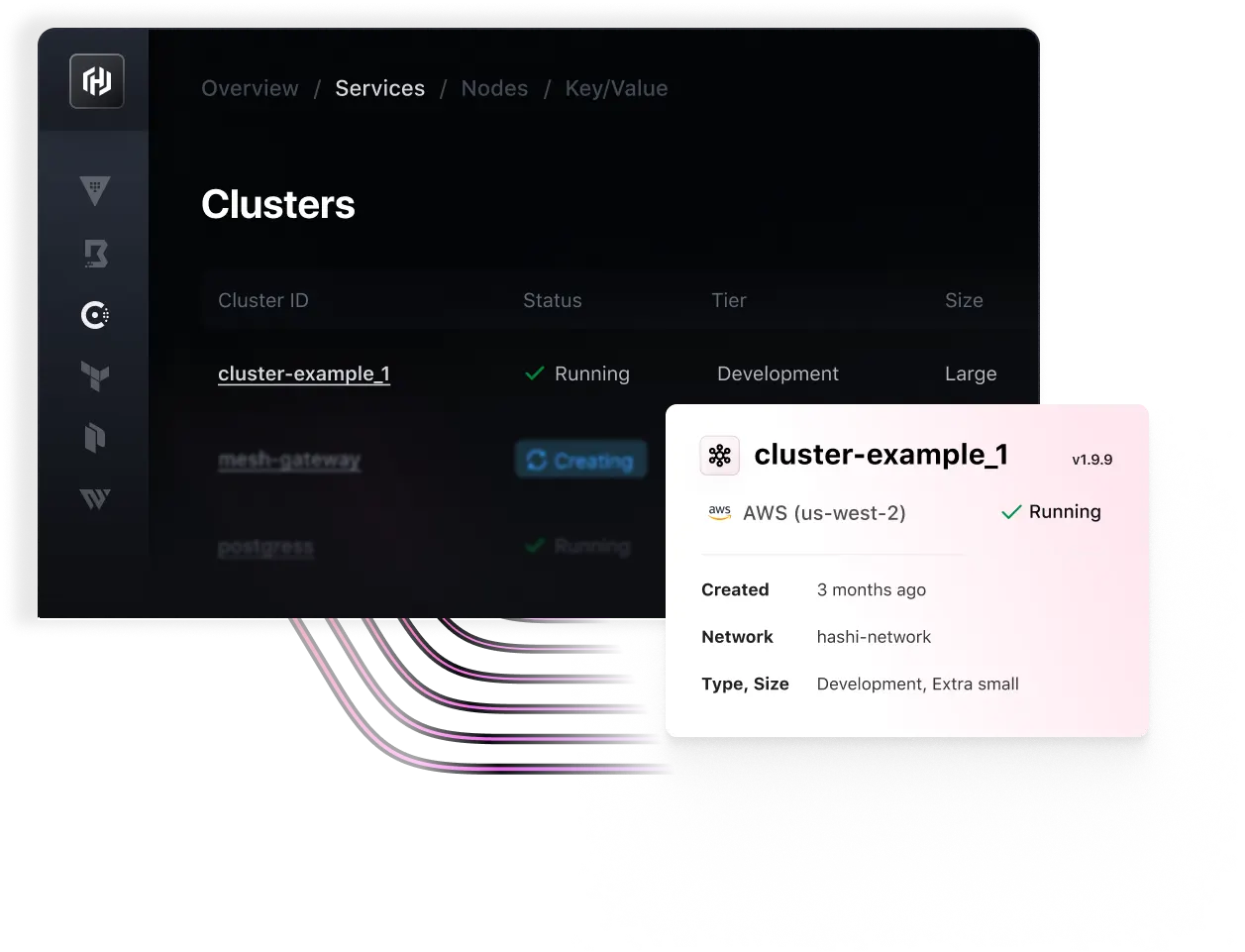
Multi-platform service discovery
Create a source of truth and real-time directory for tracking and routing services.
Global service mesh and API gateway
Global service mesh and API gateway
Global service mesh and API gateway
Reduce misconfigurations and manual ticketing for dynamic IPs.
Accelerate your cloud journey
Ready to take the next step? Connect with our sales team or get started today for free with the HashiCorp Cloud Platform.
